Cybersecurity Begins with People

Author Marc Hallquist
WannaCry – Petya – Ransomware – Phishing – DDOS. Unfortunately, these terms have entered the lexicon of the modern board room. Experts predict global annual cybercrime costs are expected to grow from $6 trillion in 2021 to $10.5 trillion by 2025.1
IT risk management and cybersecurity has gone from an underfunded IT backwater ten years ago to third on the list of Top Ten Global Business Risks, according to insurer Allianz. It has become big business. The global cybersecurity market is expected to exceed $120 billion this year. Security technologies, cyber insurance, and security staffing all require major investments.
Small to medium-size businesses have as much, or more at risk than large enterprises – and have fewer resources to work with. Spending wisely is a must. Organizations looking to maximize risk reduction return on security spending should first address the basics – People and Process. Here are the three highest-ROI investments every business can take.
1 – Develop basic security processes (before buying expensive tools)
Everyone wants a quick, easy solution. Managers are tempted to just write a check to any vendor who promises to have the magic bullet. Buying tech is one thing – effectively implementing it is something else. During the well-publicized Target breach in 2013, their high-end malware detection tools were logging alerts, but no one was monitoring them. The wise IT leader will start by focusing on a few priorities:
- Frequent, ideally automatic, patching of operating systems and basic anti-malware software
- Effective, tested, backup processes
- Effective management of network security and access permissions. In the Target breach, attackers gained access by hacking an external vendor, in turn allowing them to penetrate Target’s Point of Sale system and other assets. Common sense dictates that the credentials and access supplied to anyone be limited to the systems and services they are required to access – and no more.
2 – Take Policies seriously – and make them accessible
Many organizations are missing security policies, have poorly written policies only a sys admin can understand, or have boilerplate policies that are never really implemented.
Does everyone in your organization know WHAT your security policies and procedures are, know WHERE they are, and understand WHY policies around passwords, access, and encryption are important? It’s important to invest in making this information user-friendly and universally accessible. Task or hire someone to make this happen!
3 – Educate your people
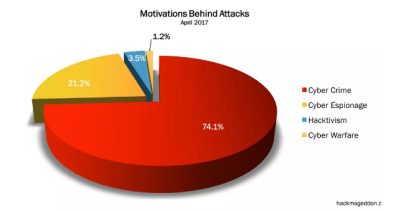
Cyber Crime motivates most attacks, as you can see in the graphic (from security site hackmageddon.com). Criminal elements aim at your most vulnerable resource – your people. Phishing attacks are getting more sophisticated and more targeted. Did the CEO really send that email requesting a wire transfer? Did the help desk really request me to type my credentials in this website? Multiple recent studies show that 30% of phishing emails get opened. These numbers can be dramatically decreased with education.
Organizations such as the Anti-Phishing Working Group and the National Cyber Security Alliance offer free ideas and tools for educating your staff. Security companies such as knowbe4 also offer excellent education products and services, some free of charge.
Once you have taken these high-ROI actions, feel free to invest in penetration testing, more sophisticated network and endpoint protection, and other measures appropriate for your level of risk tolerance. You will get more from your Technology investments having first addressed your People and Processes.
1. Cybercrime to Cost the World $10.5 Trillion By 2025. Cybercrime Magazine, November 13, 2020
Identify your path to CFO success by taking our CFO Readiness Assessmentᵀᴹ.
Become a Member today and get 30% off on-demand courses and tools!
For the most up to date and relevant accounting, finance, treasury and leadership headlines all in one place subscribe to The Balanced Digest.
Follow us on Linkedin!
